The results are in! After one month I saw 214,442 malicious login attempts to the honeypot:
Telnet made up almost half of these connections, with 99,840. Followed by SSH (60,964 connections) and VNC with 52,942 connections. We only saw about 600 HTTP/HTTPS connections, 20 FTP connections, and 10 SOCKS5 connections.
Some interesting statistics were able to be developed based on this. Keep in mind, the device never sent a single unsolicited packet outbound. All of this traffic was scanning for the device.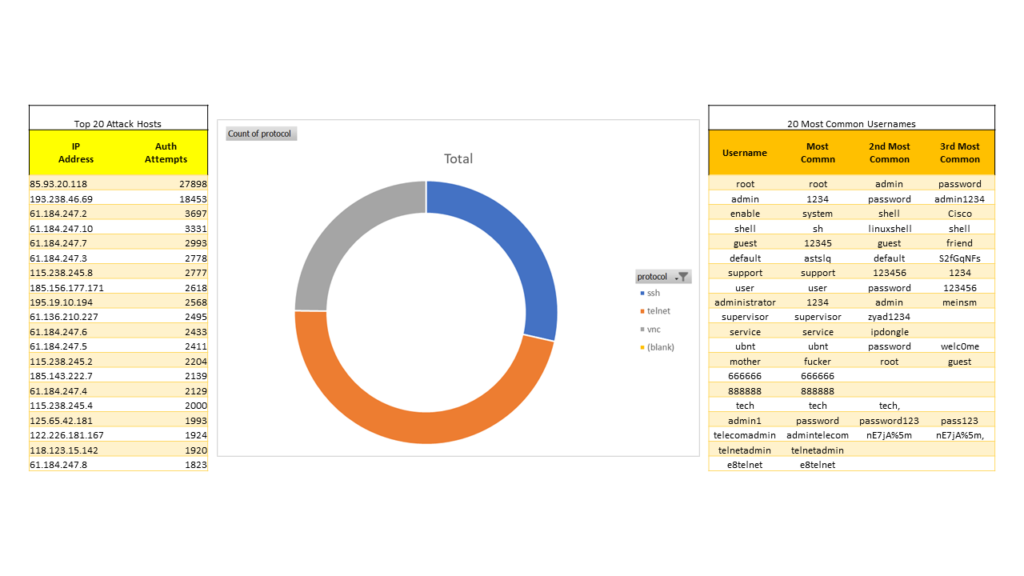
Also, you can download the full list of username and passwords or the list of attack source IPs to see every password I saw or everyone who tried to attack.
Check this list, if any of your passwords are on it, change them!!